Learn strongSwan/IKE/IPsec with decrypted packets
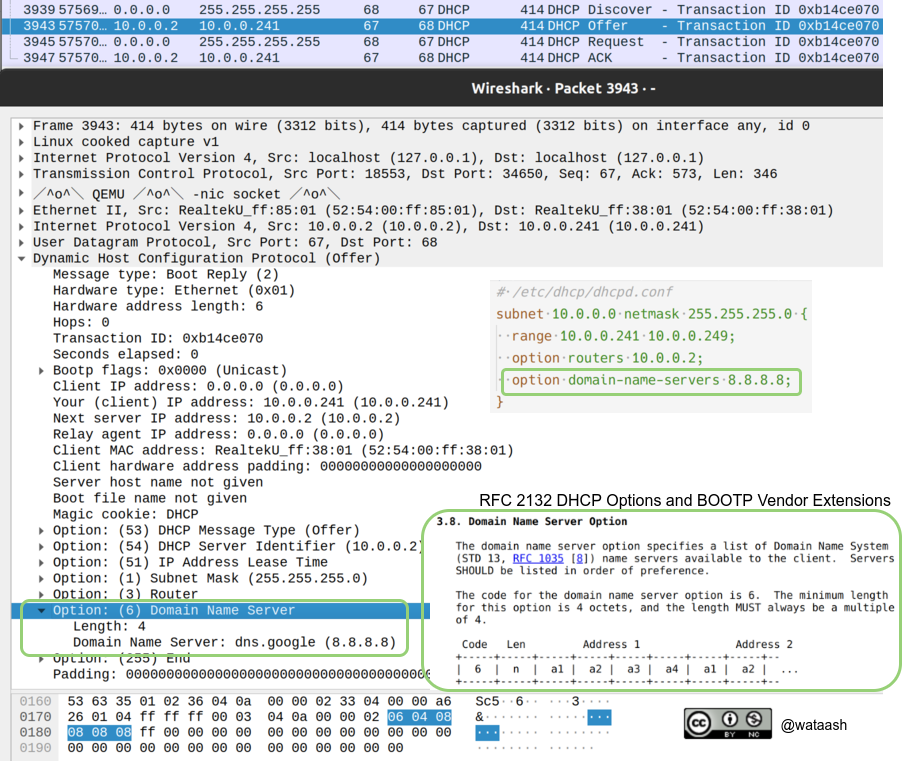
The best way to get started with a unfamiliar network protocol is to see its actual packets, the author thinks.
So the easiest way to understand a protocol is doing an experiment with it – editing the config, executing commands, and seeing the resulting packets and the client/daemon’s status. By these interactive operations, we can get a rough and intuitive understanding about the protocol efficiently. After that, we find we’ve got to be able to understand the corresponding part of the RFC.
But this approach is often impossible to be applied to IKE/IPsec, since the large part of the packets are encrypted. And sometimes IKE server rejects establishing VPN without notifying the reason, because the reason might be a hint for the attackers.
Fortunately, Wireshark have the functionality to decrypt IKEv1/IKEv2/ESP packets, and I hacked strongSwan to do the Wireshark decrypting easily.
In this article, Let’s do IKE/IPsec experiments and get insights about IKE/IPsec.
TODO
- distribute a docker image in which we can easily do IKE experiments
- experiments
- IKEv1
- quick mode/aggressive mode
- IKEv2
- NAT-traversal
- policy-based/routing-based IPsec
- ESP/AH
- rejection reasons
- cryptographic calculations (nonce, prf, integrity hash, pre-shared key, …)
- IPcomp
- IKEv1 DPD/IKEv2 keepalive
- rekey
- and more…
- IKEv1